
New – Amazon VPC Community Entry Analyzer

In case you are a member of your group’s networking, cloud operations, or safety groups, you’re going to love this new characteristic. The brand new Amazon VPC Community Entry Analyzer helps you determine community configurations that result in unintended community entry. As you will notice in a second, it’s going to level out methods that you could enhance your safety posture whereas nonetheless letting you and your group be agile and versatile. In distinction to handbook checking of community configurations, which is error inclined and arduous to scale, this software allows you to analyze your AWS networks of any measurement and complexity.
Introducing Community Entry Analyzer
Community Entry Analyzer takes benefit of our automated reasoning expertise that already powers AWS IAM Entry Analyzer, Amazon VPC Reachability Analyzer, Amazon Inspector Community Reachability, and different provable safety instruments.
This new software makes use of Community Entry Scopes to specify the specified connectivity between your AWS assets. You may get began with a set of Amazon-created scopes, after which both copy & customise them, or create your personal from scratch. The scopes are high-level and impartial of any specific community structure or configuration, and may be considered a language for specifying the correct degree of entry & connectivity to your community. You’ll be able to, for instance, create a scope to confirm that every one internet apps use a firewall to entry Web assets, or to point that AWS assets utilized by your Finance group are separate, distinct, and unreachable from the assets utilized by your Growth group.
To judge your community in opposition to a specific scope, you choose it and provoke an evaluation. It runs for a couple of minutes after which generates a set of findings, every of which signifies an surprising community path between the AWS assets outlined within the scope. You’ll be able to analyze the findings, alter your configuration or modify the scope in response to the findings, and re-run the evaluation, all in only a few minutes.
The evaluation course of examines a really big selection of AWS assets together with Safety Teams, CIDR blocks, prefix lists, Elastic Community Interfaces, EC2 cases, Load Balancers, VPC, VPC subnets, VPC endpoints, VPC endpoint companies, Transit Gateways, NAT Gateways, Web Gateways, VPN Gateways, Peering Connections, and Community Firewalls. Your scopes can use Useful resource Teams to reference all assets which are tagged in a specific manner.
Utilizing Community Entry Analyzer
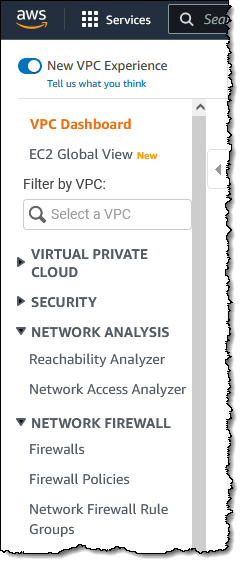
To get began, I open the VPC Console, discover the Community Evaluation part on the left-side navigation, and click on Community Entry Analyzer:
I can see all of my scopes. Initially, I’ve 4, all created by Amazon and able to use:
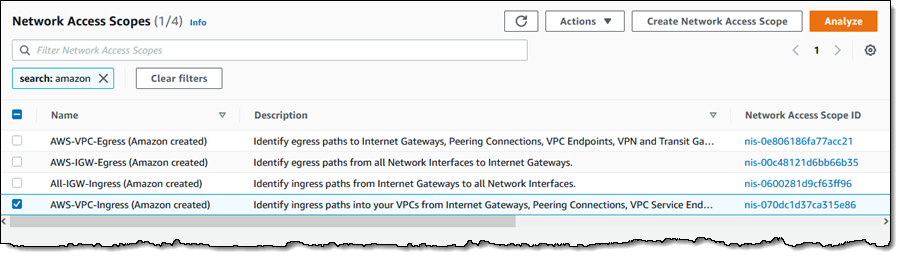
To conduct an evaluation, I choose a scope (AWS-VPC-Ingress (Amazon created)) and click on Analyze. The scope’s description reads:
“Determine ingress paths into your VPCs from Web Gateways, Peering Connections, VPC Service Endpoints, VPN and Transit Gateways.”
The evaluation runs for a few minutes and shows the findings as quickly as it’s accomplished:

There’s a whole lot of very helpful data right here! The spectrum chart gives an summary of the assets which are within the findings. I can hover my mouse over any of the segments to study extra, or click on on one with a purpose to filter the findings and present solely those who reference a specific useful resource or useful resource sort:

For instance, I click on VPC Peering Connections and I can see all the findings that reference the VPC peering connection:
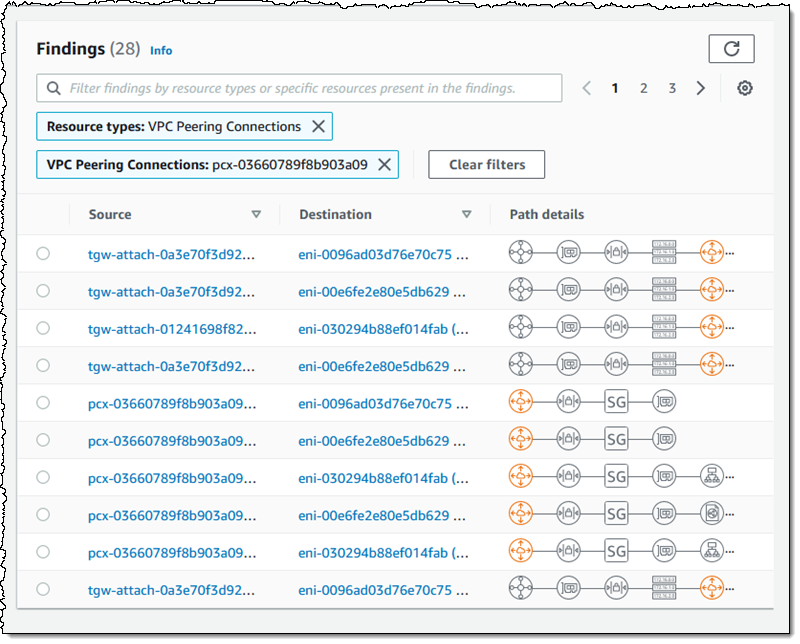
As you may see, the Path particulars spotlight the VPC peering connection within the path! The following step is to look at the findings, resolve which of them are anticipated, and so as to add them to the scope in order that they’re excluded from future findings (extra on that in a bit).
Inside a Community Entry Scope
Let’s take a fast look within the Community Entry Scope that I used above, after which construct one other scope from scratch utilizing the visible builder. Every scope is represented in JSON format, and signifies what is taken into account in-scope (acceptable) visitors between sources and locations:
The matchPaths ingredient accommodates supply and vacation spot components. Every of those components, in flip, identifies AWS useful resource varieties and particular assets. Whereas not proven right here, scopes can even comprise supply and vacation spot IP addresses, ports, prefix lists, and visitors varieties (TCP or UDP). The excludePaths can comprise useful resource varieties, particular assets, and so forth. I may, for instance, outline sources and locations that match all Web Gateway ingress visitors, however exclude visitors that flows by way of a Load Balancer, or I may exclude SSH visitors destined for my bastion cases.
Constructing a Community Entry Scope
I can construct a brand new scope in 3 ways. I can Duplicate and modify an present one, I can begin from scratch and use the visible builder, or I can write my very own JSON and use both the CLI or the API to create a scope. I click on Create Community Entry Scope to make use of the builder:
I can begin with one in every of 5 predefined templates, or I can construct my very own:

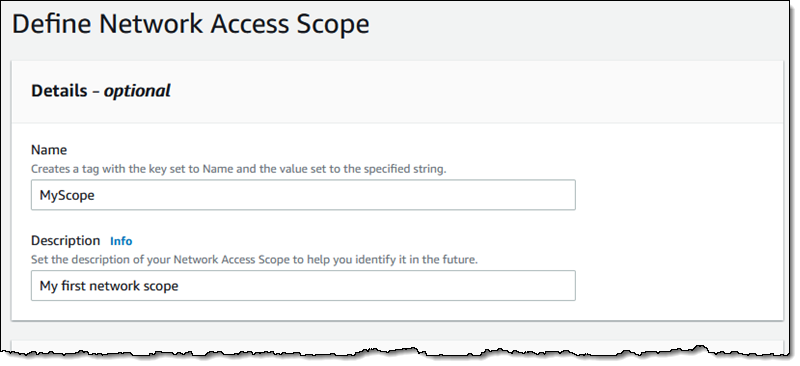
I enter a reputation and an outline:
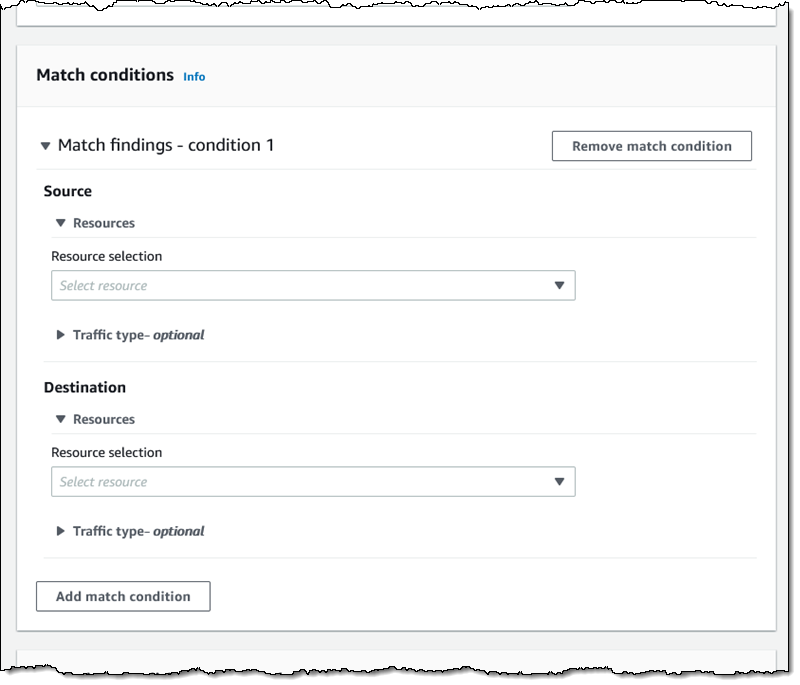
Then I outline the supply and locations by useful resource sort, id, visitors sort, and so forth:
I’ve many choices for matching the visitors sort. This enables me to create scopes for very particular functions:
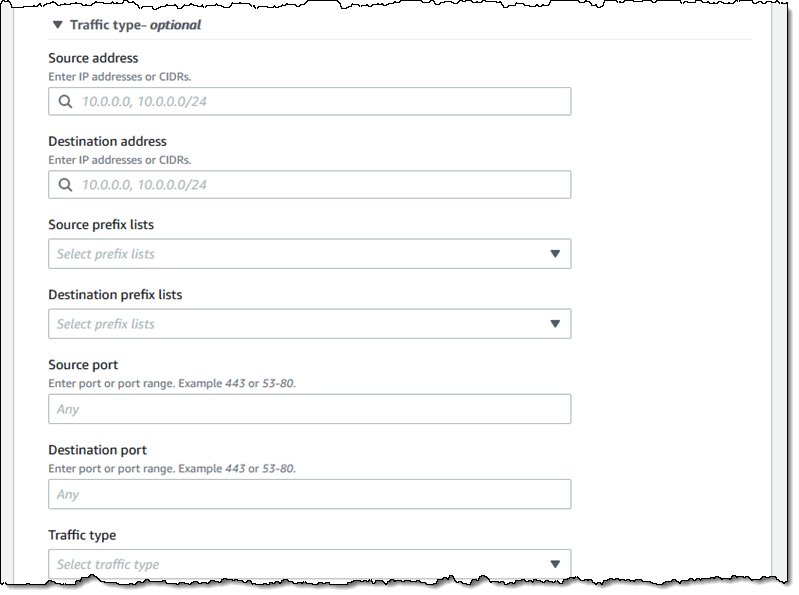
I can use the same interface so as to add any elective exclusions.
Issues to Know
It is a very highly effective software and one which I feel you’re going to love. Listed here are a few issues to find out about it:
Pricing – You pay $0.002 for every Elastic Community Interface (ENI) analyzed as a part of an evaluation.
Areas – Community Entry Analyzer is obtainable within the US East (N. Virginia), US East (Ohio), US West (N. California), US West (Oregon), Africa (Cape City), Asia Pacific (Hong Kong), Asia Pacific (Mumbai), Asia Pacific (Seoul), Asia Pacific (Singapore), Asia Pacific (Sydney), Asia Pacific (Tokyo), Canada (Central), Europe (Frankfurt), Europe (Eire), Europe (London), Europe (Milan), Europe (Paris), Europe (Stockholm), South America (São Paulo), and Center East (Bahrain) Areas.
Within the Works – We now have numerous further options on the product roadmap together with assist for AWS Organizations, the power to run your analyses on an everyday schedule, and assist for IPv6 handle ranges and assets.
— Jeff;















